 You can’t turn on the TV, listen to talk radio or read a tweet without hearing about companies, hospitals, and even government agencies being victimized by some type of cyber-crime. You would think that in 2018 our computers and business systems would be secured from outside, and inside, threats. So, what’s the deal and why does this keep happening?
You can’t turn on the TV, listen to talk radio or read a tweet without hearing about companies, hospitals, and even government agencies being victimized by some type of cyber-crime. You would think that in 2018 our computers and business systems would be secured from outside, and inside, threats. So, what’s the deal and why does this keep happening?
Four Words: Communicating Via the Internet
In the 'Wild West' paced development of apps, software, email, texting, setting up wide area networks and local area networks, everyone "jumped in" without a lot of thought about “bad guys.” Nor how these tools would evolve to help them, especially, when “network security” has been somewhat vague in its definition. All companies, hospitals, and government agencies have SOME level of network security but don’t seem to build security from the ground up, or even worse, know where their vulnerabilities lie.
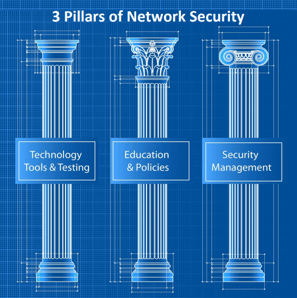
3 Pillars of Network Security
Technology tools and testing: You are only as secure as your oldest piece of hardware, software or non-patched application.
A Security Risk Analysis allows you to outline your security strengths and vulnerabilities as well as provides your IT team critical information regarding gaps in your current security plan. Non-disaster testing of your backups, business continuity plans, and security tools will dramatically save you from downtime and data loss.
Education and policies: You are only as secure as your least educated employee.
Actions, policies, and procedures to manage your workforce in relation to protecting your company’s proprietary information and access to that information. Covers training procedures for all employees, vendors and 3rd parties who have direct access to your systems.
Security Management: Diligent, dedicated and documented on-going management is critical
There is no “set it and forget it feature” for network security. Ongoing monitoring, auditing and managing of systems is the only way to create a secure environment. Additionally, “easy fixes” like securing the physical the structures and electronic equipment used in the day to day workings of your business are often overlooked.
You can have secure networks - by focusing on your security. Network security is created with technical tools, education plans, employee policies, their enforcement and security management and testing.
Who in your organization is responsible for your networks’ security planning, management, and maintenance?
If you don’t know or don’t have someone, your immediate step is to assign that task to a C-level person as they will need access to resources and time to dedicate to overseeing the security of your business. Their first order of business is to “know what you don’t know” in order to determine your system’s strengths and vulnerabilities. Print our “Network Security Blueprint” to help be a guide in this process.


